Windows File System Access and Change Auditing Windows Server/Workstation
CPTRAX for Windows
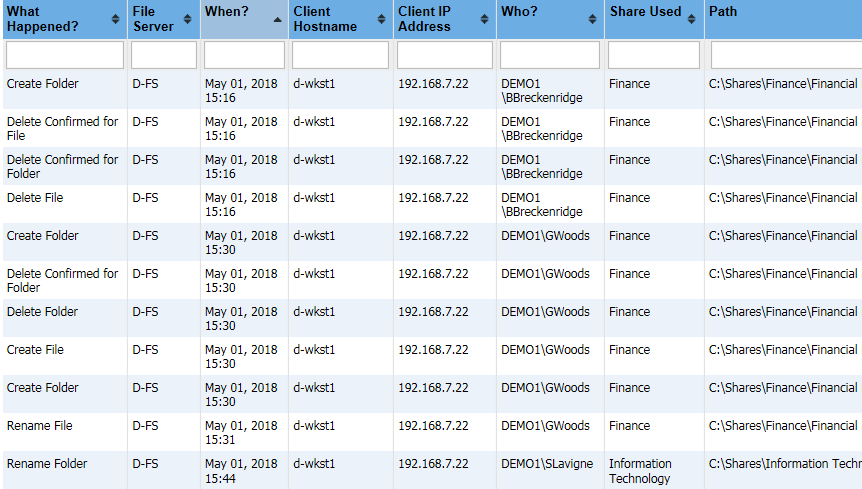
- Track access and changes to file shares, folders, and files
- Identify username, workstation, and IP address of user file activity
- Receive email alerts when actions of interest occur
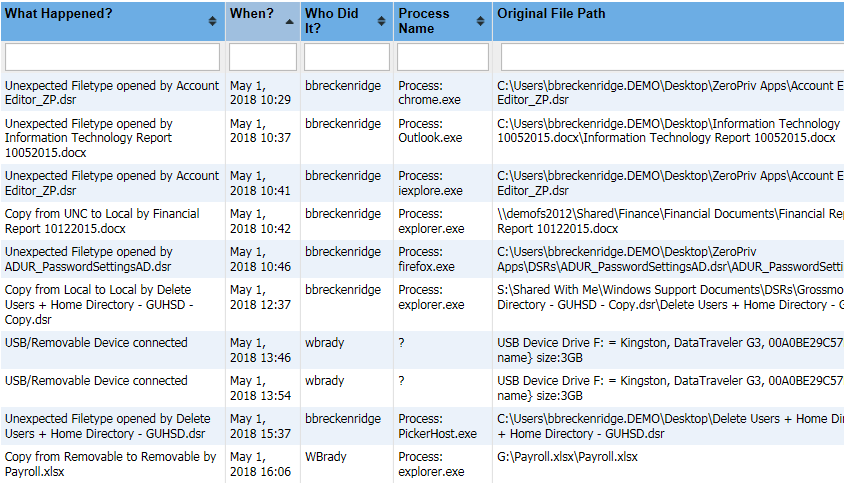
- Track files copied to USB, uploaded via web browser or attached to an email
- Detect and automatically stop malicious activity - Learn More
Track access and changes to file shares, folders, and files on Windows servers
CPTRAX enables real-time Windows file system access and change auditing for Windows Servers. Audit file system changes as they occur and quickly provide auditors with the file activity details they need.
Audit these file and folder activities:
- Opens
- Creates
- Renames/Moves
- Deletes
- Modifications
- Permission changes
- Ownership changes
Track Windows workstation file activity:
- Block files from being created on USB/removable device
- Block files from being copied to USB/removable device
- Email alert based on amount of data copied
- Email alert when removable device is connected to workstation
- Track files copied to removable device (USB, DVD/CD, Hard Drive)
- Track when files are created on a removable device
- Track when removable device is connected/disconnected
- Track when files are deleted from a removable device
- Track local file copies
- Track when files are copied from a server to a workstation
- Track when files are created on a public share
- Track when files are modified on a public share
- Track when an application opens an unexpected file type including:
- What files are being uploaded from a web browser
- What files are being attached to an email
- Report on removable devices present when agent is started
Detail information about who is accessing and changing files, including:
- Username (LDAP or SAM account name)
- Workstation name
- Workstation IP address
- File/Folder path
- Share used for access
- Security identifier (SID)
- Remote computer name (for Remote Desktop and Terminal server sessions)
- Remote computer IP address (for Remote Desktop and Terminal server sessions)
Real-time email alerts
Know immediately when an action of interest occurs. CPTRAX can send you and your staff an email when certain file activities occur, while
quietly auditing everything else.
Quickly Detect and Automatically Stop Threats
Detect threats with Pattern alerts which can be configured to alert you when interesting actions occur repeatedly on your Windows servers such as mass file deletions or ransomware behavior. Optionally call a PowerShell script to immediately stop the action from happening. Learn More
Other features
- Customizable tracking profiles
- Central management console
- Automated report scheduling
- Centralized log files
- Encrypted Log Files
- Send log data to Microsoft SQL Server (Optional)
- Send event messages to Syslog Server (Optional)
Get a free trial of CPTRAX for Windows today!
CPTRAX includes 1 YEAR of our world class support!
Assisted Installation
Our team will help you implement CPTRAX from start to finish.
Unlimited Training
We'll make sure you can get the information you need out of CPTRAX.
Unlimited Support
Our rapid-response support team can assist with any questions you may have.